In our security and firewall services offered to customers for whom business continuity is of great importance, in addition to special devices positioned for service delivery and software produced specifically for the job, services are also obtained from major internet operators.
Netinternet aims to ensure that all management in all technically possible areas of the services provided is in the hands of our users in order to offer the best service experience. Voxility is one of the operators from which we receive services for DDoS prevention purposes. Netinternet allows you to view/edit IP management in terms of firewall, attack reports, and attack logs for your IP addresses announced in Voxility systems from your customer panel.
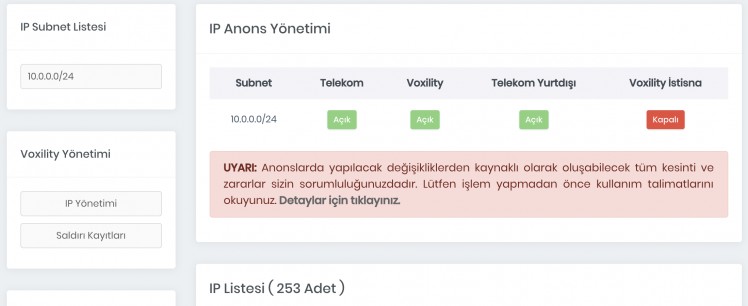
If you have a Firewall service and your IP address is announced at the Voxility operator, you can see the Voxility Management table in the Applications > IP Management section of your Netinternet customer panel. You must switch to IP Management to change the DDoS protection options for your IP addresses, and to Attack Records to view DDoS attacks launched towards your IP addresses and access log records.
IP Management
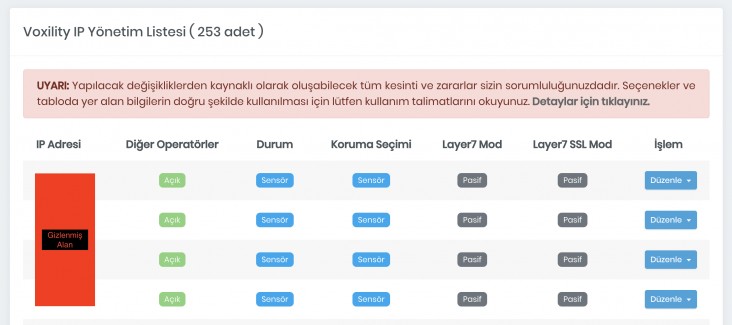
Allows you to view the list of IPs under your management along with protection options as shown in the table above. The meanings of the data in the table are below;
Other Operators: More than one operator provides data center internet access. If other operators related to your IP address appear as “Open”, it means your IP announcements are not only made through Voxility, therefore attacks that may come through other operators connected to the data center will not be filtered through Voxility. However, when your IP announcements are announced through Voxility, all access outside of Turkey passes through Voxility.
Status: Shows the current service status, can take two values as “Sensor” or “Always-on”. Sensor indicates that DDoS filtering is not being done, but that it will switch to active protection, i.e., Always-on mode, if any DDoS is initiated. Always-on shows that all incoming requests are filtered regardless of what they are.
Protection Selection: Can take two values as “Sensor” or “Always-on” at your choice. Sensor does not filter incoming requests, only provides protection when DDoS is initiated; Always-on filters all incoming requests regardless of what they are. Constantly using Always-on may slow down your network traffic and cause errors. We do not recommend constant use of Always-on mode. In extraordinary situations, you can manually activate the protection mode this way.
Layer7 Mode: Provides protection at Layer7 level. The best protection is provided with this mode being active, and having the Layer7 service active also slightly slows down network traffic. When Layer7 is active, while simple http-get attacks are blocked with session control, all file transfers towards your network are also protected at the network level against known viruses, trojans, backdoors, sql injection and similar malware and requests.
Layer7 SSL Mode: Allows the same features as Layer7 to be applied to encrypted SSL traffic as well. For this, you need to perform the “SSL Setup” operation through the “Edit” menu. If you do not do this, a default but non-valid SSL certificate will be used in place of SSL certificates used in all your encrypted traffic. You can define one SSL for each IP address.
Operation: You can upload the necessary files for “SSL Setup” through the “Edit” menu in the operations table, and change the “Protection Selection”, “Layer7 Mode”, “Layer7 SSL Mode” options in the table through the “Options” section.
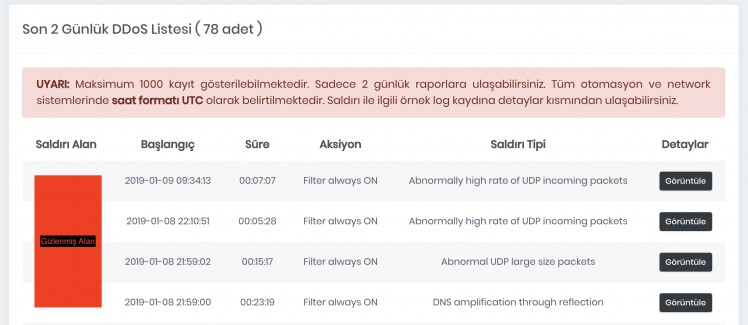
Attack Records
This section lists DDoS attacks launched towards IP addresses in the selected IP range in your IP management in the last 2 days. The meanings of the data in the table are below;
Attack Recipient: Shows the IP address under attack in the selected IP range.
Start: Shows the date the attack started in UTC format. You need to add +3 hours to evaluate according to Turkey time.
Duration: Indicates the duration of the attack; if the attack is ongoing, it shows this additionally with the “Ongoing” statement in the duration table.
Action: Shows the filtering method of the attack. This table takes the values “Filter ON”, “Filter always ON”. Filter ON shows a transition from sensor mode, Filter always ON shows a transition from continuous protection.
Attack Type: This is the technical information screen about the incoming attack. It is for professional users.
Details: A sample 300-line log record related to the incoming attack is displayed from the “View” section in this table. A sample view is below.
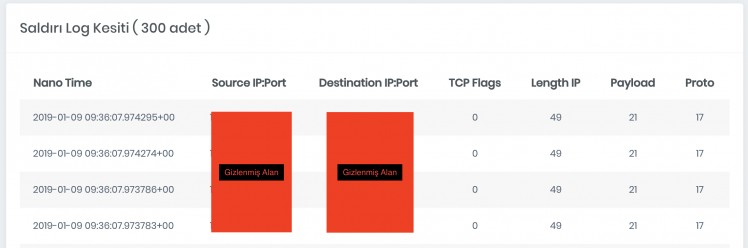
The meanings of the data in the table for the sample log record displayed above are below;
Nano Time: Shows the time the log record was taken in UTC format in nanoseconds.
Source IP:Port: Shows the IP address from which the attack was initiated and the outgoing port.
Destination IP:Port: Shows the IP address under attack and the port.
Other Fields: For professional users. “TCP Flags”, “Length IP”, “Payload”, “Proto”
Leave a Comment
* Your comment will be published after approval.






Comments
0No comments yet. Be the first to comment!